标签:ciscn MISC number 初赛 flag output line range matrix
ez_usb
打开流量包观察后发现在2.4.1,2.8.1,2.10.1三个流里有HID Data,于是分别导出,并用
tshark -T json -r xxx.pcapng > xxx.json
和
strings xxx.json | grep usb.capdata
来导出hiddata(不知道为啥这里不可以直接用tshark导出usbdata)
简单处理后使用脚本处理生成键盘敲击内容
#!/usr/bin/env python
# -*- coding:utf-8 -*-
normalKeys = {"04":"a", "05":"b", "06":"c", "07":"d", "08":"e", "09":"f", "0a":"g", "0b":"h", "0c":"i", "0d":"j", "0e":"k", "0f":"l", "10":"m", "11":"n", "12":"o", "13":"p", "14":"q", "15":"r", "16":"s", "17":"t", "18":"u", "19":"v", "1a":"w", "1b":"x", "1c":"y", "1d":"z","1e":"1", "1f":"2", "20":"3", "21":"4", "22":"5", "23":"6","24":"7","25":"8","26":"9","27":"0","28":"<RET>","29":"<ESC>","2a":"<DEL>", "2b":"\t","2c":"<SPACE>","2d":"-","2e":"=","2f":"[","30":"]","31":"\\","32":"<NON>","33":";","34":"'","35":"<GA>","36":",","37":".","38":"/","39":"<CAP>","3a":"<F1>","3b":"<F2>", "3c":"<F3>","3d":"<F4>","3e":"<F5>","3f":"<F6>","40":"<F7>","41":"<F8>","42":"<F9>","43":"<F10>","44":"<F11>","45":"<F12>"}
shiftKeys = {"04":"A", "05":"B", "06":"C", "07":"D", "08":"E", "09":"F", "0a":"G", "0b":"H", "0c":"I", "0d":"J", "0e":"K", "0f":"L", "10":"M", "11":"N", "12":"O", "13":"P", "14":"Q", "15":"R", "16":"S", "17":"T", "18":"U", "19":"V", "1a":"W", "1b":"X", "1c":"Y", "1d":"Z","1e":"!", "1f":"@", "20":"#", "21":"$", "22":"%", "23":"^","24":"&","25":"*","26":"(","27":")","28":"<RET>","29":"<ESC>","2a":"<DEL>", "2b":"\t","2c":"<SPACE>","2d":"_","2e":"+","2f":"{","30":"}","31":"|","32":"<NON>","33":"\"","34":":","35":"<GA>","36":"<","37":">","38":"?","39":"<CAP>","3a":"<F1>","3b":"<F2>", "3c":"<F3>","3d":"<F4>","3e":"<F5>","3f":"<F6>","40":"<F7>","41":"<F8>","42":"<F9>","43":"<F10>","44":"<F11>","45":"<F12>"}
output = []
keys = open('x.txt')
for line in keys:
try:
if line[0]!='0' or (line[1]!='0' and line[1]!='2') or line[3]!='0' or line[4]!='0' or line[9]!='0' or line[10]!='0' or line[12]!='0' or line[13]!='0' or line[15]!='0' or line[16]!='0' or line[18]!='0' or line[19]!='0' or line[21]!='0' or line[22]!='0' or line[6:8]=="00":
continue
if line[6:8] in normalKeys.keys():
output += [[normalKeys[line[6:8]]],[shiftKeys[line[6:8]]]][line[1]=='2']
else:
output += ['[unknown]']
except:
pass
keys.close()
flag=0
print("".join(output))
for i in range(len(output)):
try:
a=output.index('<DEL>')
del output[a]
del output[a-1]
except:
pass
for i in range(len(output)):
try:
if output[i]=="<CAP>":
flag+=1
output.pop(i)
if flag==2:
flag=0
if flag!=0:
output[i]=output[i].upper()
except:
pass
print ('output :' + "".join(output))
处理后发现,2.4.1里无信息,2.8.1里的是一个rar压缩包,2.10.1里的不知道是什么,打开压缩包之后发现有密码,猜测2.10.1里内容是密码,于是成功打开压缩包,里面就是flag
everlasting_night(好像非预期了)
使用在线图片一把梭网站,上传后发现两个密码
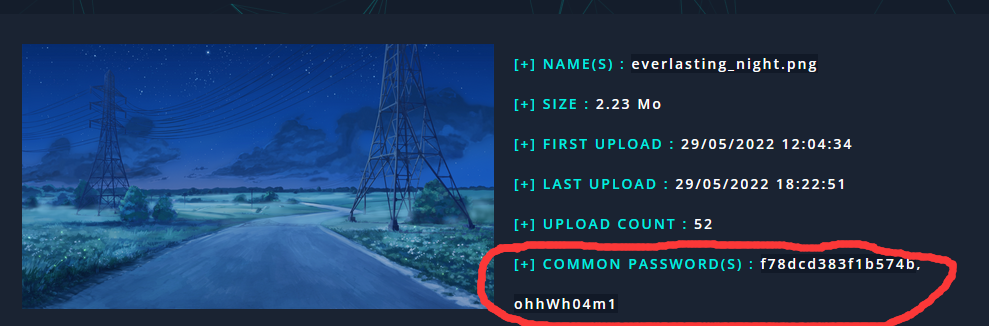
然后根据提示使用cloacked-pixel脚本解密
python2 lsb.py extract everlasting_night.png 1.txt f78dcd383f1b574b
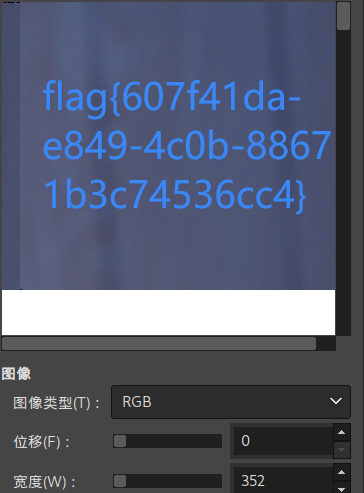
发现是个zip压缩包,再使用第二个密码ohhWh04m1打开压缩包发现flag文件,改后缀为data后用gimp打开随便调调宽度就有flag
babydisk
磁盘取证,直接上取证大师,结果如下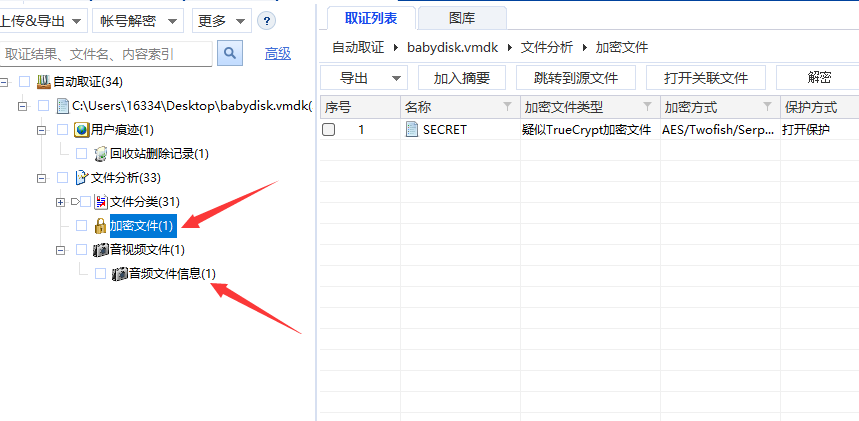
发现一个加密文件和一个wav音频文件,导出后分析出加密文件是一个veracrypt,暂时没有密码,就先放着,去分析音频。分析发现音频有deepsound信息,于是使用john爆破deepsound密码
python3 deepsound2john.py voipNewRing.wav > 1.txt
john 1.txt
爆破很快,得到密码是feedback,拿去用deepsound解密得到一个key.txt
内容是e575ac894c385a6f,于是将其作为密码去用veracrypt,得到一个文件叫“spiral”,搜了一下是螺旋的意思,winhex打开发现文件头像zip格式但是文件尾以及文件整体都怪怪的,上网查查发现有个算法叫螺旋算法,代码比较简单,分析一下又发现这个spiral文件大小是7569字节,刚好是87的平方,可以凑一个矩阵,所以写脚本解密
def function(n):
matrix = [[0] * n for _ in range(n)]
number = 1
left, right, up, down = 0, n - 1, 0, n - 1
while left < right and up < down:
# 从左到右
for i in range(left, right):
matrix[up][i] = number
number += 1
# 从上到下
for i in range(up, down):
matrix[i][right] = number
number += 1
# 从右向左
for i in range(right, left, -1):
matrix[down][i] = number
number += 1
for i in range(down, up, -1):
matrix[i][left] = number
number += 1
left += 1
right -= 1
up += 1
down -= 1
# n 为奇数的时候,正方形中间会有个单独的空格需要单独填充
if n % 2 != 0:
matrix[n // 2][n // 2] = number
return matrix
f = open('spiral','rb').read()
k = function(87)
k = sum(k,[])
arr = [0]*7569
for i in range(len(k)):
arr[i] = f[k[i]-1]
for i in arr:
print(hex(i)[2:].zfill(2),end='')
再把解密出的正确顺序的hex处理成一个压缩包,打开后发现一个图片
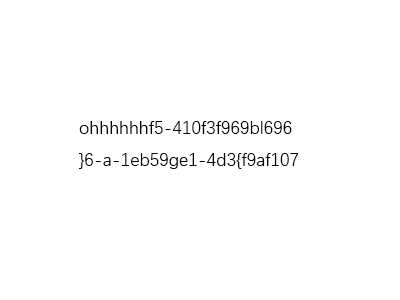
发现连着前面的ohhhhhh刚好是49个字符,于是还是螺旋,就可以得到flag
标签:ciscn,MISC,number,初赛,flag,output,line,range,matrix 来源: https://www.cnblogs.com/zysgmzb/p/16327773.html
本站声明: 1. iCode9 技术分享网(下文简称本站)提供的所有内容,仅供技术学习、探讨和分享; 2. 关于本站的所有留言、评论、转载及引用,纯属内容发起人的个人观点,与本站观点和立场无关; 3. 关于本站的所有言论和文字,纯属内容发起人的个人观点,与本站观点和立场无关; 4. 本站文章均是网友提供,不完全保证技术分享内容的完整性、准确性、时效性、风险性和版权归属;如您发现该文章侵犯了您的权益,可联系我们第一时间进行删除; 5. 本站为非盈利性的个人网站,所有内容不会用来进行牟利,也不会利用任何形式的广告来间接获益,纯粹是为了广大技术爱好者提供技术内容和技术思想的分享性交流网站。
